Why You Need BIMI and VMC in Your Email Deliverability Toolkit

Email authentication is a connection between the sender email domain (e.g., success@yourdomain.com) and the email service provider (ESP) sending email on behalf of your domain. Having authentication is the first thing servers look for when deciding to bounce, quarantine or route your email to the intended recipient. It is the main thing that differentiates a legitimate email sender from a spammer.
Spam organizations and spam fighting technologies have been doing the tango since email became a thing. Back in the day, email was the wild west until there was so much spam that email systems needed to filter email traffic. The filter criteria factored in the use of one or more of the following email authentication methods:
- Sender Policy Framework (SPF)
- Domain Key Identified Mail (DKIM)
- Domain Message Authentication, Reporting and Conformance (DMARC)
Many brands still outsource lead generation to email lead gen companies. These lead gen companies use a collection of acquisition domains (e.g., greatoffer.com, promotion.com) and IP addresses, and they DO use all of the above authentication methods to have the best chance of reaching an inbox. This means that servers have a difficult time determining what is a legitimate email and a spam email if they both use all authentication methods. This also means that spam will still reach your inbox.
Spammers 1 – Email Recipients 0
So, what now? How can you know if the email you’re receiving is in fact from the brand you think it’s from?
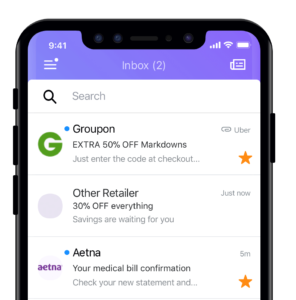
Now there is a visual indicator, a brand’s logo, that can be displayed in the inbox and only the brand owner can implement this type of authentication. It’s called Brand Indicators for Message Identification (BIMI).
BIMI Prerequisites Checklist:
- For a BIMI logo to display properly to an email recipient, the sender needs to use all three authentication methods listed above.
- The DMARC policy txt record on the DNS is set at enforcement; and either “p=quarantine” or “p=reject”
- Publish a BIMI record for the domain in the Domain Name System (DNS)
Once all prerequisites are handled, the next step is to work with a Mark Verifying Authority (MVA), an organization that provides evidence of logo ownership. If the logo ownership is validated, the brand receives a Verified Mark Certificate (VMC).
Before an email ever reaches an inbox of a recipient, the recipient’s mail server will first look for the presence of SPF, DKIM and DMARC from the sending server. If found, the server then checks if there is a valid BIMI record, validates the record and if also verified by the VMC, the BIMI logo can be displayed next to the message in the inbox. This visual indicator gives email recipients the comfort that the email in their inbox is from who it says it’s from.
Spammers 0 – Email Recipients 1
